two keys
Asymmetric cryptography uses two keys: if you encrypt with one key, you may decrypt with the other. Hashing is a one-way cryptographic transformation using an algorithm (and no key).
How many keys are used in symmetric?
one key
Symmetric encryption is a type of encryption where only one key (a secret key) is used to both encrypt and decrypt electronic information. The entities communicating via symmetric encryption must exchange the key so that it can be used in the decryption process.
Does symmetric or asymmetric have larger keys?
Symmetric encryption is more secure than asymmetric encryption when you use smaller key sizes (such as a 256-bit key). That’s because in asymmetric encryption that uses smaller keys, having the public key actually makes the private key easier to calculate. (This is why we use larger keys in asymmetric encryption.)
How many keys would they all need for asymmetric vs symmetric encryption?
two key
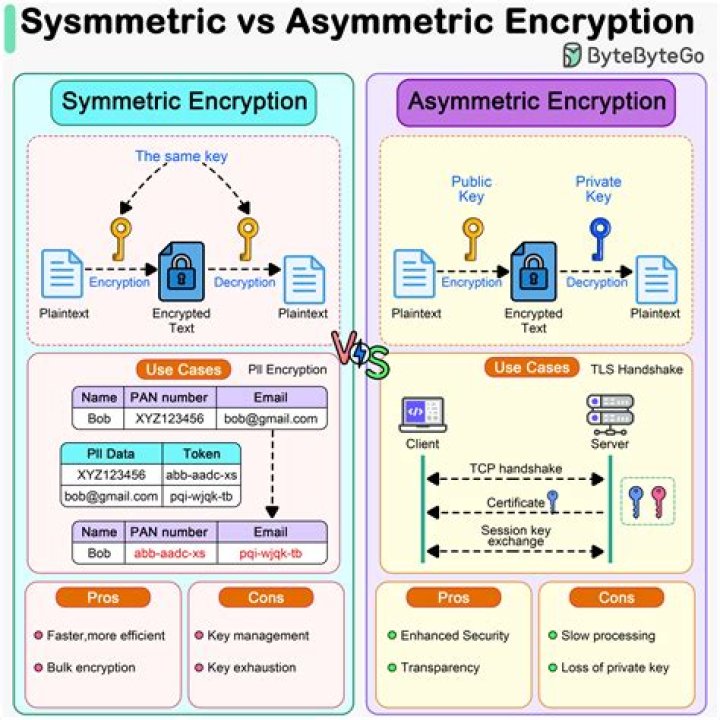
Difference Between Symmetric and Asymmetric Key Encryption
| Symmetric Key Encryption | Asymmetric Key Encryption |
|---|---|
| It only requires a single key for both encryption and decryption. | It requires two key one to encrypt and the other one to decrypt. |
How many keys are used with public key cryptography?
Public key encryption uses two different keys. One key is used to encrypt the information and the other is used to decrypt the information. Sometimes this is referred to as asymmetric encryption because two keys are required to make the system and/or process work securely.
How many keys are used in cryptography?
In public key cryptography, we use two keys: one for encryption and the second for decryption. We can distribute the public key everywhere without compromising the private key.
How many keys are used by group of 4 people if they are using symmetric key cryptography?
Two key-issuance session keys, one for each party (short-lived); A shared session key for the conversation (short-lived).
How many asymmetric keys are there?
two
Difference between Symmetric and Asymmetric Encryption
| Symmetric Encryption | Asymmetric Encryption |
|---|---|
| Symmetric encryption consists of one of key for encryption and decryption. | Asymmetric Encryption consists of two cryptographic keys known as Public Key and Private Key. |
What is the difference between symmetric and asymmetric algorithms?
Symmetric encryption uses a single key that needs to be shared among the people who need to receive the message while asymmetric encryption uses a pair of public key and a private key to encrypt and decrypt messages when communicating.
What is the difference between a symmetric key system and an asymmetric key system?
The basic difference between these two types of encryption is that symmetric encryption uses one key for both encryption and decryption, and the asymmetric encryption uses public key for encryption and a private key for decryption.
How many secret keys are used by group of 4 people if they are using symmetric key cryptography techniques for communication?
In symmetric-key cryptography, Each pair of users require a unique secret key. If N people in the world want to use this technique, then there needs to be N(N-1) / 2 secret keys.
How many keys are required if two parties communicate using asymmetric cryptography?
In asymmetric (public key) cryptography, both communicating parties (i.e. both Alice and Bob) have two keys of their own — just to be clear, that’s four keys total.